Filters
Filters
Close filters

Audio
Article
Insurance and Risk Management: Why the Traditional Playbook No Longer Works
View Article

Audio
Article
How Dataverse Becomes the Data Layer Your AI Strategy Needs
View Article

Audio
R&D
AI-Assisted Prototyping: When Figma Falls Short and Cursor Takes Over
View Article

Audio
Article
Why Most AI Initiatives Fail — and How Power Platform Turns AI into Measurable Business Outcomes
View Article

Audio
Article
Operating in an Age of Permanent Instability: Keeping Organisations Running in Conflict Zones and Crisis Conditions
View Article
Audio
Article
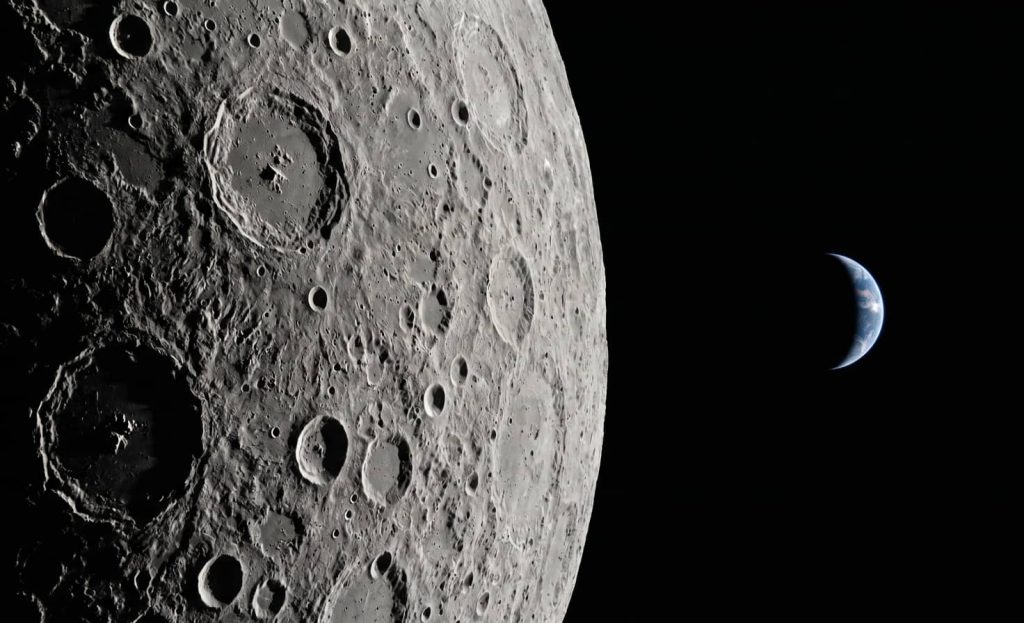
AI in Space Exploration: What NASA’s Artemis II Reveals About Building Mission-Critical Intelligent Systems
View Article

Audio
Article
Why AI-Native Development Teams Keep Getting Their Estimates Wrong — and How to Fix It
View Article

News
ELEKS Earns Top-Tier Scores in 2026 IAOP® Global Outsourcing 100® Evaluation
View News
Audio
Article
The End of Traditional SDLC: What the Claude Browser Extension Delivers for QA (Part 3)
View Article
Audio
Article
The End of Traditional SDLC: A Working AI QA Prototype and What It Means for the Team (Part 2)
View Article





















